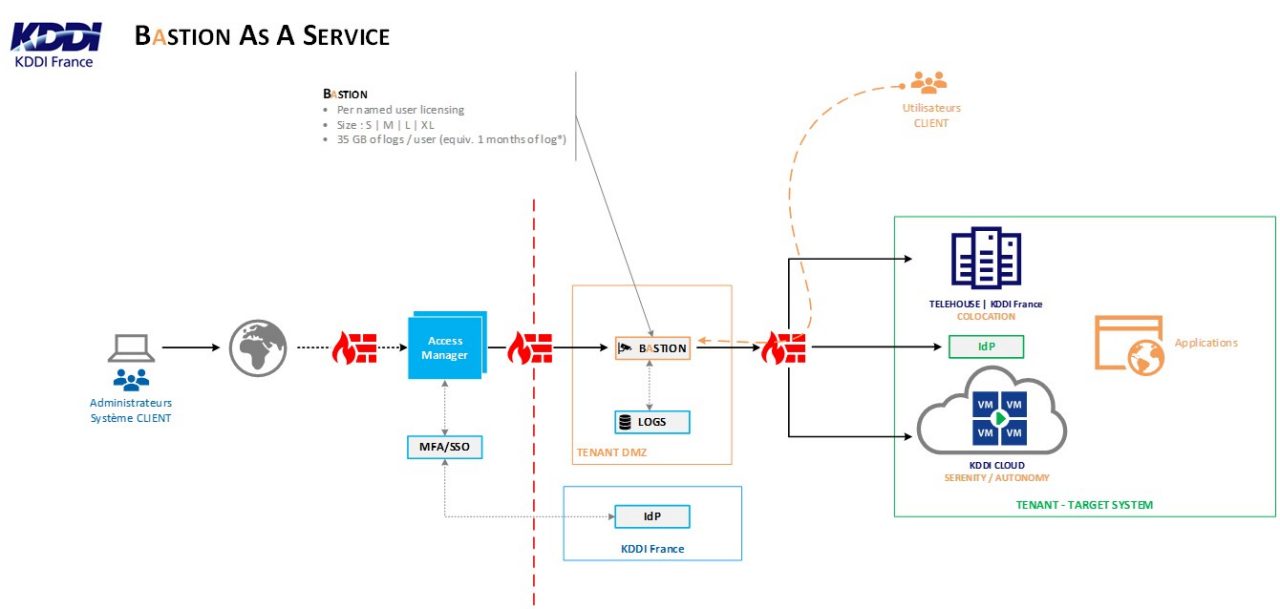
KDDI Cyber Bastion, in partnership with Wallix, is a service offering that provides a single, robust, centralized and auditable entry point to your infrastructure without the need to use a VPN tunnel, client software, or open ports on your firewalls.
KDDI Cyber Bastion — Privileged Account Management
The various key features

Zero Trust Secure Access
Access to servers (Windows or Linux), databases, and various company applications is simple and can be achieved from any HTML5-compatible browser. This approach ensures optimal accessibility, whether from a desktop or laptop, regardless of the operating system.
No additional plugins, agents, or components are required: everything operates directly through the browser, significantly simplifying deployment and maintenance. Updates are centralized and require no intervention on user workstations.
Furthermore, users do not need to know the passwords for privileged accounts. Access is managed securely and centrally, reducing the risks associated with the disclosure of sensitive credentials and strengthening compliance with security policies.
This solution thus combines ease of use, enhanced security, and operational efficiency.

Granular Secure Access
The solution relies on enhanced access using the "least-privilege" principle, ensuring that each user has only the rights necessary for their tasks.
Permissions are structured by role to ensure clear and controlled access management.
Security is strengthened through IP whitelisting, strong authentication (2FA), and automatic password rotation for sensitive accounts.
These combined mechanisms significantly reduce the risk of unauthorized access while ensuring simple and secure administration.

Session recordings and auditables
Each session is fully logged to ensure complete traceability of all actions performed.
This feature allows for the precise reconstruction of operations and the rapid identification of the source of an incident, if necessary.
In addition, a command interception and control mechanism is in place to prevent malicious actions or actions that violate security policies. Sensitive commands can be blocked, thus reducing the risks associated with errors, privilege abuse, or account compromises.

User Management
Administrators have a centralized interface that allows them to manage all users and access policies for target systems. They can create, modify, or delete accounts, assign roles, and adjust permission levels according to operational needs.
Access policy management allows for precise definition of who can access which resources, under what conditions, and according to which security rules.
The different dimensions of the bastion
Bastion host sizing is determined by the number of simultaneous sessions it needs to accommodate, in order to guarantee optimal performance and a smooth user experience. It's important to note that a single user can open multiple sessions in parallel.
| Size | Nomber of sessions RDP / SSH | CPU, RAM, DISK, OS |
|---|---|---|
| Bastion S | 25 / 240 | 4, 16 Go, 50 Go |
| Bastion M | 40 / 240 | 8, 16 Go, 50 Go |
| Bastion L | 50 / 480 | 8, 32 Go, 50 Go |
| Bastion XL | 75 / 480 | 16, 32 Go, 50 Go |
- Storage volume is in addition to the size of the Bastion host.
- Estimated storage for session recording: ~35 GB / User / month, based on 3 hours of connection per day over 5 business days, 4 weeks per month.
- Windows Server RDS (SAL RDS) licenses are not included.
Log management and rotation
| Configuration option | Défault value | |
|---|---|---|
| Delete user data older than | 36 weeks | |
| Delete user logs older than | 5 weeks | |
| Delete sessions older than | 36 months | |
| Delete the sessions below the free space | 10% | |
| Prefer sessions older than | 15 days | |
| Keep the most recent critical sessions | 7 days |
Recommendations for safety measures
To ensure enhanced protection of cloud environments, it is essential to implement security measures tailored to different platforms and architectures. These recommendations aim to limit the risks of unauthorized access, strengthen network traffic control, and ensure effective isolation of critical resources.
KDDI Cloud Serenity
For the KDDI Cloud Serenity offering, it is recommended to enable the OS-level firewall with "least privileges." In practical terms, this means that only strictly necessary traffic is allowed, namely SSH and RDP connections originating from the bastion host. This approach limits the server's exposure to external threats and significantly reduces the attack surface, while still allowing legitimate administrators to perform their management tasks.
KDDI Cloud Autonomy
For the KDDI Cloud Autonomy offering, the use of micro-segmentation between virtual machines is a key security measure. East-West filtering restricts SSH and RDP communications to only authorized connections, thus limiting the potential spread of internal attacks. This granular isolation between VMs strengthens internet network security and prevents uncontrolled access between resources, while maintaining the flexibility required for daily operations.
Why is Bastion as a Service ?
The bastion host serves as a secure access point between users and target systems. It centralizes SSH and RDP connections, controls access, and logs sessions for enhanced security and traceability.
Contact an expert
Got a question? Looking to outsource your infrastructure?
Need some specific information?
Our expert consultants are on hand to help!
"Ensure reliable backups and uninterrupted business operations with our tailored cyber protection solutions.
Ideal for organizations with on-premises infrastructure, our offering delivers dependable backups and an effective Disaster Recovery Plan (DRP)."
Related Case Studies